- Server operating system version
- Debian 10.13
- Plesk version and microupdate number
- 18.0.60 Update #1
Hi,
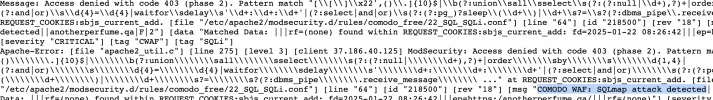
I just created new subdomain. I didn't do anything on that page but I already get forbidden 403 code. I found out that Web Application Firewall (builtin from Plesk) threw the error:
It's a blank page with a default index.html file. Should I be worried that my Plesk-instance may be infected? Or is this a know issue and I have to remove the rule 218500?
Do you also have such issue?
Best regards
Floh
I just created new subdomain. I didn't do anything on that page but I already get forbidden 403 code. I found out that Web Application Firewall (builtin from Plesk) threw the error:
Code:
ModSecurity: Access denied with code 403 (phase 2). Pattern match "[\\\\[\\\\]\\\\x22',()\\\\.]{10}$|\\\\b(?:union\\\\sall\\\\sselect\\\\s(?:(?:null|\\\\d+),?)+|order\\\\sby\\\\s\\\\d{1,4}|(?:and|or)\\\\s\\\\d{4}=\\\\d{4}|waitfor\\\\sdelay\\\\s'\\\\d+:\\\\d+:\\\\d+'|(?:select|and|or)\\\\s(?:(?:pg_)?sleep\\\\(\\\\d+\\\\)|\\\\d+\\\\s?=\\\\s?(?:dbms_pipe\\\\.receive_message\\\\ ..." at REQUEST_COOKIES:sbjs_current_add. [file "/etc/apache2/modsecurity.d/rules/comodo_free/22_SQL_SQLi.conf"] [line "64"] [id "218500"] [rev "18"] [msg "COMODO WAF: SQLmap attack detectedDo you also have such issue?
Best regards
Floh