We are Blocking a Bruteforce with Fail2Ban and i discovered that sometimes the IPs are not blocked after the maxretry or the IP is found after ban.
We have set the maxretry to 3 :
[ssh]
enabled = true
filter = sshd
action = iptables[name=SSH, port=ssh, protocol=tcp]
iptables-allports[chain="INPUT", name="default", port="ssh", protocol="tcp", blocktype="REJECT --reject-with icmp-port-unreachable", returntype="RETURN", lockingopt="-w", iptables="iptables <lockingopt>"]
logpath = /var/log/secure
maxretry = 3
but when i check the logs i can see that sometime, the same ip is found more than 3 times :
/var/log/fail2ban.log:
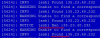
grep "Failed pass" /var/log/secure:

Can someone help us with this?
We have set the maxretry to 3 :
[ssh]
enabled = true
filter = sshd
action = iptables[name=SSH, port=ssh, protocol=tcp]
iptables-allports[chain="INPUT", name="default", port="ssh", protocol="tcp", blocktype="REJECT --reject-with icmp-port-unreachable", returntype="RETURN", lockingopt="-w", iptables="iptables <lockingopt>"]
logpath = /var/log/secure
maxretry = 3
but when i check the logs i can see that sometime, the same ip is found more than 3 times :
/var/log/fail2ban.log:
grep "Failed pass" /var/log/secure:
Can someone help us with this?
